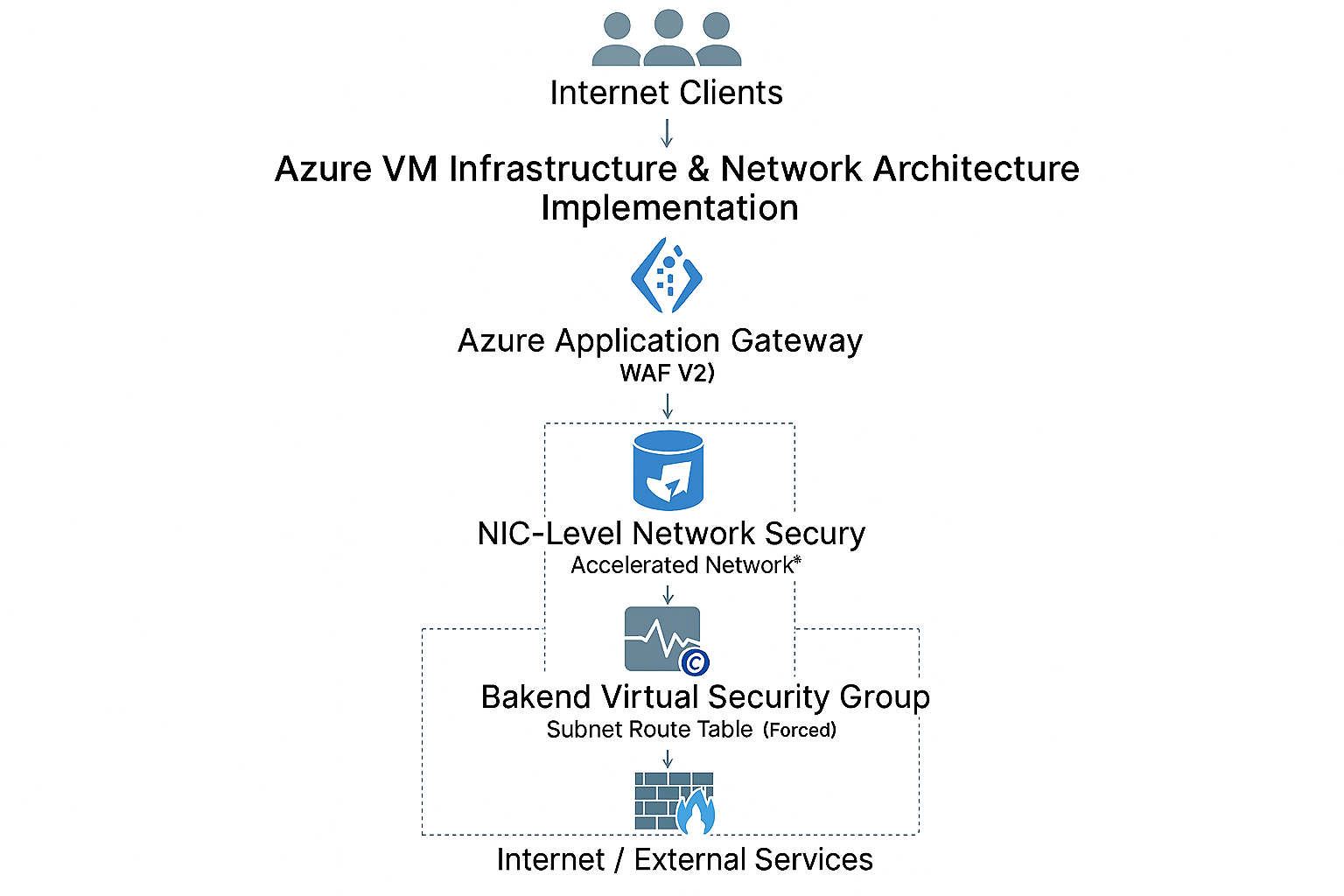
Azure VM Infrastructure & Network Architecture Implementation
This project documents the design, implementation, configuration, and validation of an existing Azure virtual machine environment. My role focused on operationalizing Azure-native networking and security components, integrating them together, and validating end-to-end traffic flow and enforcement within a production environment.
Environment Context
- Windows Server virtual machine deployed within a private Azure virtual network
- No public IP address assigned to the workload
- Accelerated networking enabled to support production performance requirements
- Infrastructure implemented within a governed enterprise Azure environment
Environment diagram
Ingress Implementation (Application Gateway & WAF)
External application access is implemented through an Azure Application Gateway configured with WAF v2. I worked within the established design to configure backend pools, routing rules, and integration with the private virtual machine, ensuring only approved HTTPS traffic reached the workload.
- Azure Application Gateway (WAF v2) deployed in a dedicated gateway subnet
- Public-facing frontend IP terminating HTTPS traffic
- Backend pool integration with private virtual machine
- HTTPS routing rules validated through production testing
Network Security Configuration (NSG)
Network Security Groups were configured at the network interface level to enforce per-workload security controls. I implemented and validated inbound and outbound rules to ensure the virtual machine only accepted intended application traffic.
- NIC-level NSG applied directly to the virtual machine
- Inbound access restricted to HTTPS (TCP/443)
- Azure infrastructure and gateway traffic explicitly permitted
- All other inbound access explicitly denied
Egress Control & Forced Routing
Outbound network flow was implemented using a subnet-level route table that forces all internet-bound traffic through a centralized security appliance. I validated routing behavior to confirm workloads could not bypass egress inspection.
- User-defined route table applied to the workload subnet
- 0.0.0.0/0 routed to a virtual appliance for outbound inspection
- No direct outbound internet access from the subnet
Firewall & NAT Configuration
Azure Firewall was used as the centralized egress and NAT boundary. I supported firewall policy configuration, validated NAT behavior, and confirmed outbound traffic was inspected and logged according to organizational security standards.
- Azure Firewall (Standard SKU) deployed in a dedicated firewall subnet
- Outbound SNAT performed through the firewall public IP
- No inbound DNAT configured at the firewall layer
- Firewall policies applied for egress control and threat intelligence filtering
Validated End-to-End Traffic Flow
Internet Clients
↓
Azure Application Gateway (WAF v2)
↓
Backend Pool Configuration
↓
NIC-Level Network Security Group (HTTPS only)
↓
Private Virtual Machine (Accelerated Networking)
↓
Subnet Route Table (Forced Routing)
↓
Azure Firewall (Inspection & SNAT)
↓
Internet / External Services
Outcome
This project is a hands-on implementation and validation of enterprise Azure networking and security services. The work emphasizes practical cloud engineering skills, operational awareness, and the ability to reason about layered security controls in an enterprise production environment.